Welcome › Forums › Integrations › Microsoft Graph Integration (includes Azure AD logs)
- This topic has 0 replies, 1 voice, and was last updated 7 years ago by
Mike Riforgiate.
Viewing 1 post (of 1 total)
- AuthorPosts
- July 3, 2018 at 9:02 pm #1667
Mike Riforgiate
KeymasterCreate the App in Azure
- https://portal.azure.com/#blade/Microsoft_AAD_RegisteredApps/ApplicationsListBlade
- Click New registration
- Name it WitFoo Precinct (MS Graph)
- Select who can use the application (access the API)
- Select Web and enter the Redirect URI as https://PrecinctIP/v1/api/azure_auth (Note: replace PrecinctIP with the IP address or FQDN of your Precinct appliance)
- Click “Register”
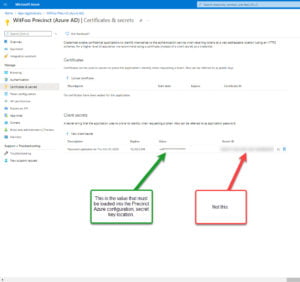
- Under Certificates & secrets click New client secret (give it a description and expiration, then click Add)
- Save the Secret ID
- Go to API permissions.
- Click on Microsoft Graph, Application Permissions, and add the following:
- Auditlog.Read.All
- DeviceManagementManaged.Read.All
- DeviceManagementManaged.ReadWrite.All
- Directory.Read.All
- SecurityAlert.Read.All
- SecurityAlert.ReadWrite.All
- SecurityEvents.Read.All
- SecurityIncident.Read.All
- User.Read
- User.Read.All
- Click on Microsoft Graph, Application Permissions, and add the following:
- Click Update permissions (Making sure the status shows each permission is granted for your organization)
- make sure to click “Grant admin consent”

Configure WitFoo Precinct
- Go to Admin->Integrations
- Click the + and select Microsoft Graph Integration
- Paste the Application (client) ID, Secret key and Tenant ID
- NOTE: Tenant ID can be found by navigating to Azure Portal > Azure Active Directory > Properties
- Click Save
-
This topic was modified 9 months, 3 weeks ago by
Kevin Sheahan. Reason: add permissions for Microsoft Intune data
-
This topic was modified 9 months, 3 weeks ago by
Kevin Sheahan. Reason: fix syntax
-
This topic was modified 8 months, 4 weeks ago by
Mike Riforgiate.
-
This topic was modified 6 months, 1 week ago by
Mike Riforgiate.
-
This topic was modified 6 months, 1 week ago by
Mike Riforgiate.
- AuthorPosts
Viewing 1 post (of 1 total)
- You must be logged in to reply to this topic.